By Morgan Greene and India Sayer Open-source software (OSS) refers to software whose source code is freely available for anyone to view, modify, and distribute. Open-source software has gained popularity over the years due to its purported benefits. However, as with any technology, it presents challenges to consider prior to adoption. One of the most touted benefits of open-source software is that it’s “freeâ€. Organizations can download,...
Read MoreThe 2022 Blueforce Texas Road Show
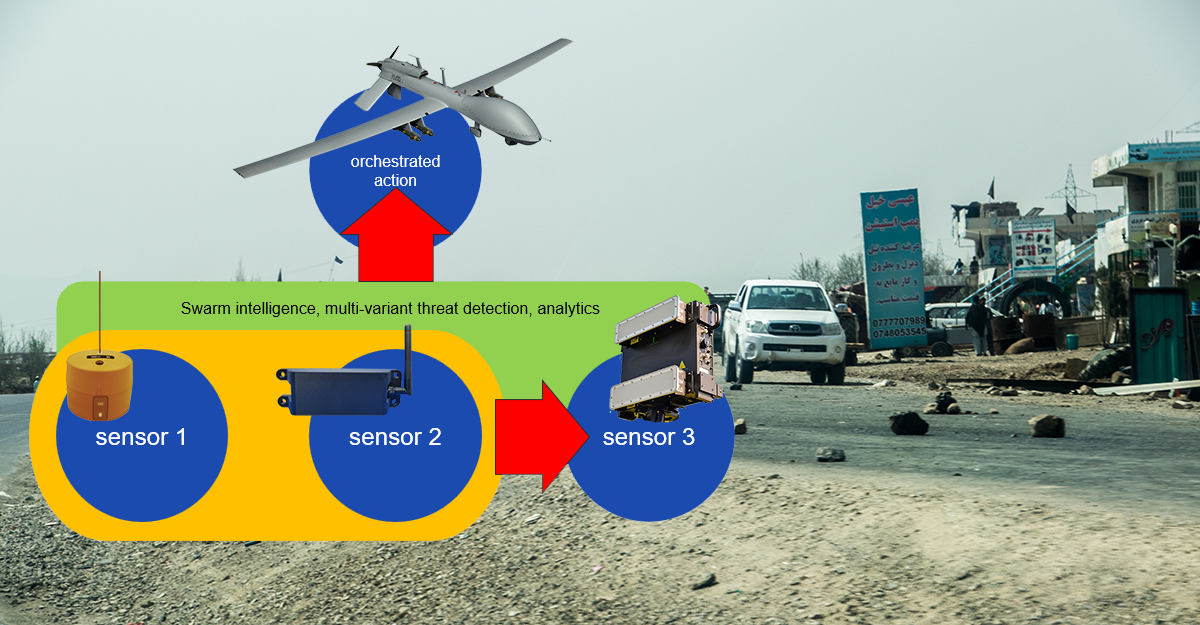
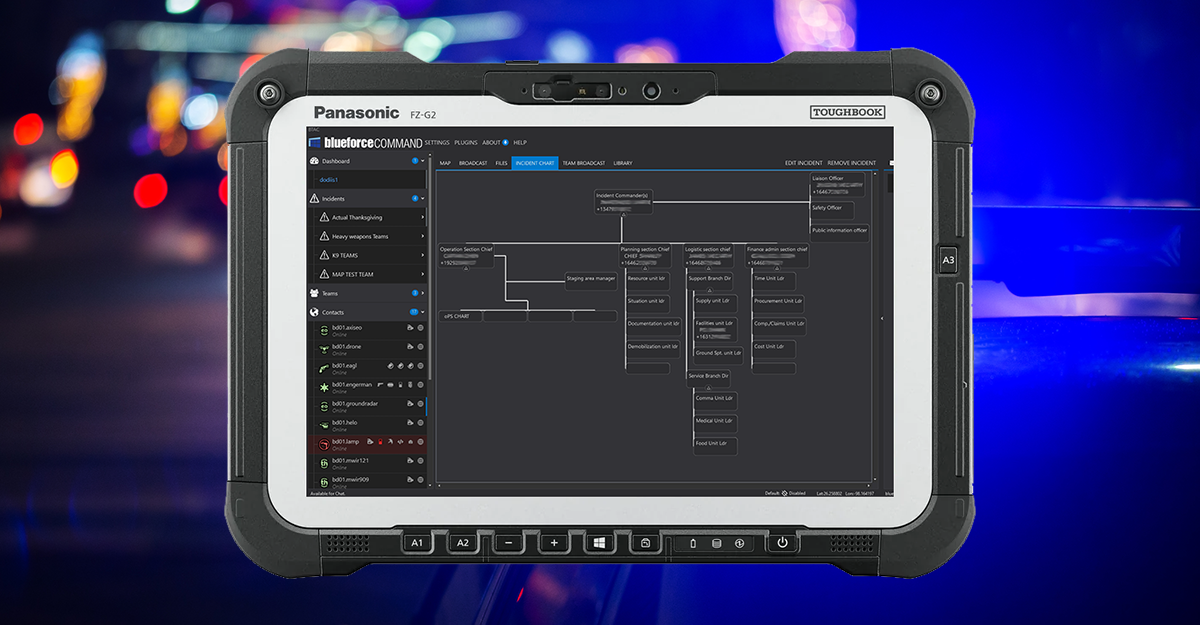
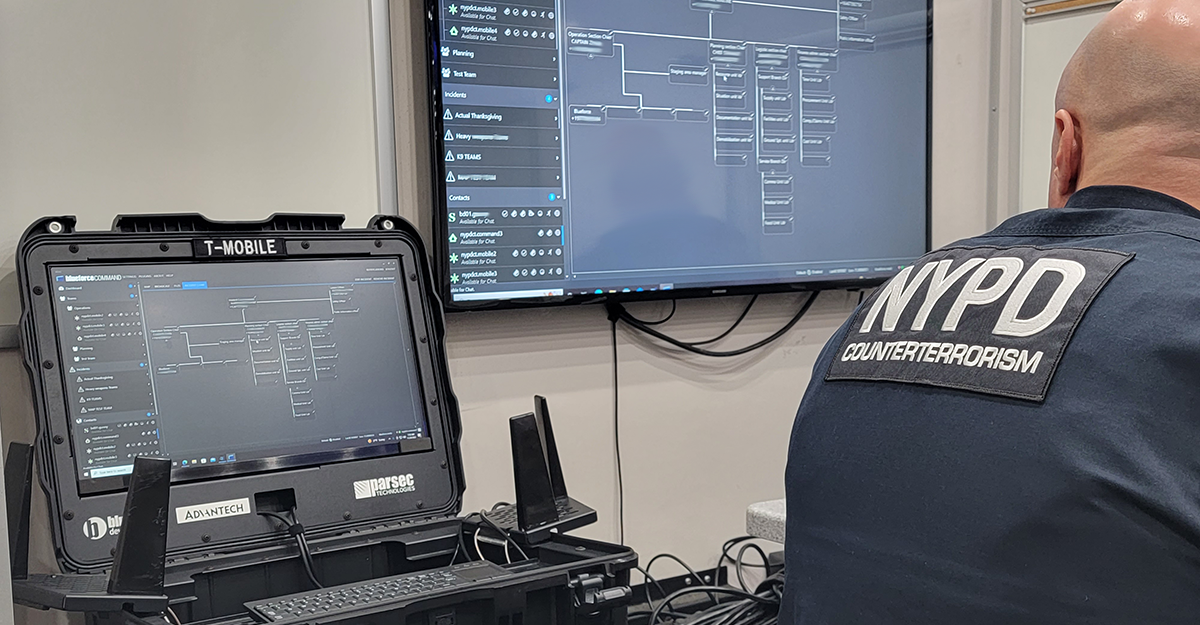
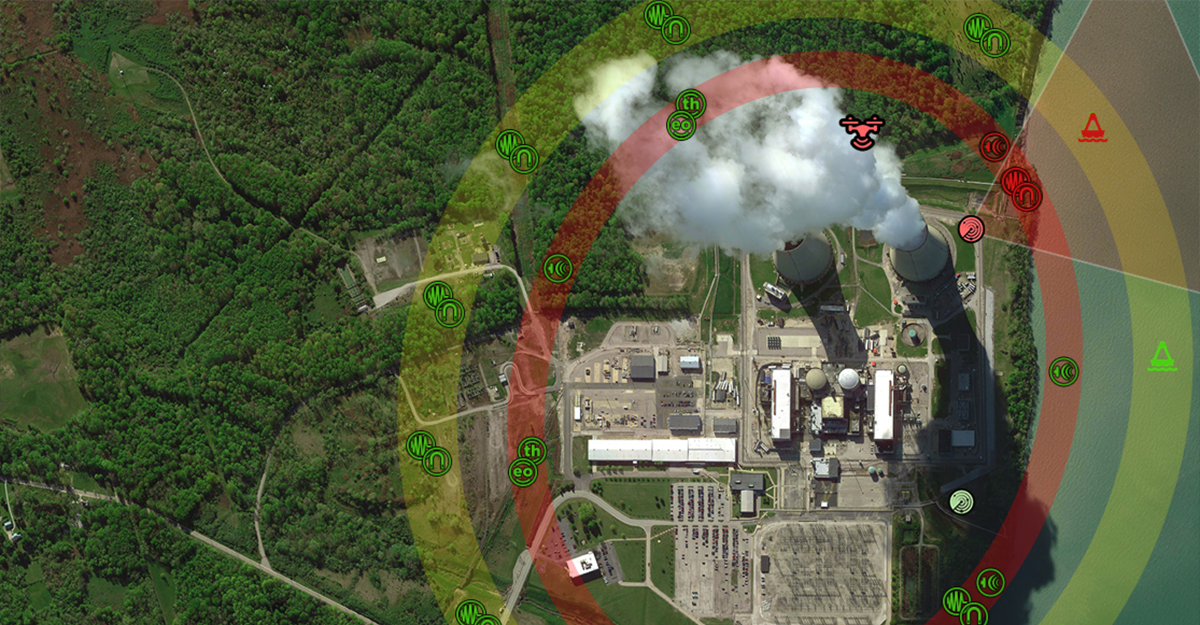
The 2022 Blueforce Texas Road Show gives you hands-on access to the latest in Public Safety, Safe Campus, and Autonomous Platform technologies. The Road Show kicks off Tuesday October 11, 2022 in Houston. For more information, click here…